A Monetary Layer for the Internet
| Crypto Words has moved! The project has migrated to a new domain. All future development will be at WORDS. | Go to WORDS |
A Monetary Layer for the Internet
By Thib
Posted April 24, 2019
Source: Wikimedia
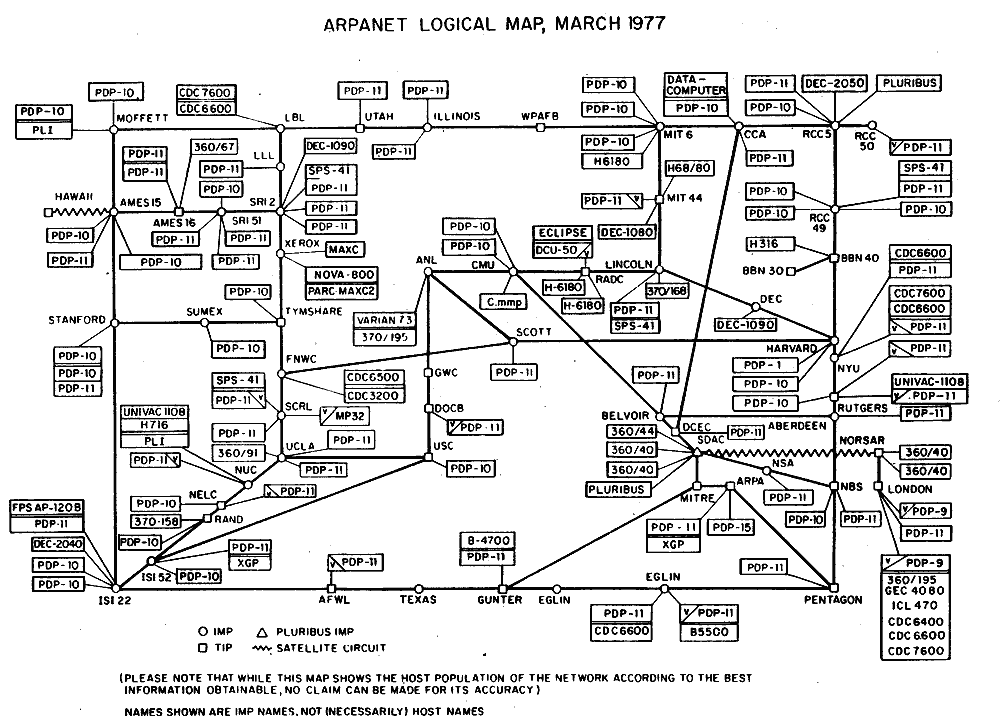
ARPANET’s First Mark into Networked Computing
Created in February 1958, the Advanced Research Projects Agency (ARPA) was a response to the Soviet launch of Sputnik 1, the first artificial Earth satellite, to research and develop projects in technology and science, beyond direct US military applications. Bob Taylor, an ARPA computer scientist convinced a colleague to support a research project using funding from a ballistic missile defense program. Following three years of research, the ARPANET project was launched as the first network to connect two geographically-distinct computers. In 1969, on October 29th at 10:30 PM PST, the first successful message ‘LO ‘ was sent from UCLA in Los Angeles to Stanford in Silicon Valley. The message was supposed to be ‘LOGIN ‘ but the system crashed. Over 7 years later, Queen Elizabeth II was sending her first email from a computer installed in the UK. The ARPANET was morphing into a small but fast-growing global network of connected computers.
Rising Computer Network Protocols
The ARPANET was the first public implementation of TCP/IP, two major protocols that now form an integral part of the Internet Protocol Suite. Taken together, this suite constitutes what we know as “the Internet”, the global interconnected network that hundreds of millions of humans use daily without ever being aware of it.
As additional computer nodes joined the ARPANET in different countries, novel technologies were developed to make the growing network more usable, notably standard network protocols.
Public computer protocols were created to govern how data is created, exchanged and interpreted between clients and servers on the same interconnected network, including Simple Mail Transfer Protocol (SMTP) to send and receive emails, File Transfer Protocol (FTP) to exchange and read files or Hypertext Transfer Protocol (HTTP) to structure and display web pages that we browse today.
HTTP is one of the most well-known public protocols. It turned ARPANET into the World Wide Web that is now commonly called the Internet or the web and established a standard for computers to communicate on the application layer of the Internet, having built on other layers of public protocols and open-source technologies.
The Internet’s Onion Shape
The Internet is built in layers, abstracted in a framework called the Open Interconnection System (OSI) model. It is a logical construction that defines network communication used by various computer systems that interact with each other.
As the Internet morphed into a more sophisticated global network of computers, the OSI model was published to help decouple seven distinct layers of public protocols useful in the creation, exchange and interpretation of data flows.
As a hierarchical system, public computer network protocols coordinate how data moves across the Internet’s seven layers. Each layer is solely responsible for performing assigned tasks and transferring completed tasks to the next layer for further processing.
This clear specialization ensures performance, reliability and scalability of the Internet.
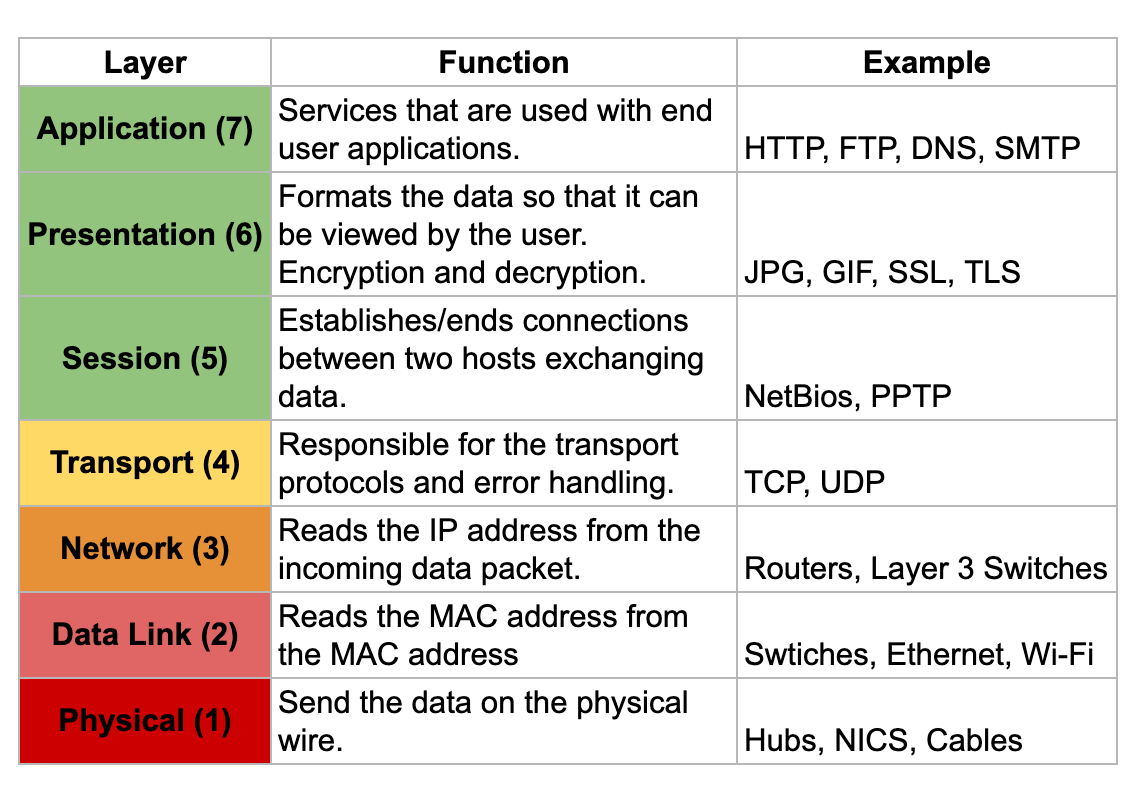 Source: Cloud Scanner
Source: Cloud Scanner
The Internet is a multi-layered global distributed network of computers that we use every day for many things without ever questioning its existence. Though only 20 years old, the Internet powers an immense amount of trades between an ever-growing number of consumers, companies and nations, accounting for roughly $28 trillion in 2016.
Long before Amazon was a thing, in 1972, students from Stanford and MIT conducted the first ever online transaction using ARPANET. The first good ever sold on the Internet was marijuana.
Many projects followed as commercial and academic attempts to create electronic cash making commerce native on the Internet. All incommensurably failed from the late 1980s to the early 2000s, including B-money, Digicash, Hashcash, and BitGold.
Technology, regulation and centralisation prevented mainstream digital currencies from ever taking off.
The Missing ‘Monetary Layer’ of the Internet
Regardless, for users to directly trade with geographically-distinct neighbours on the Internet, one essential component has been absent: a monetary layer to store, exchange and measure value natively on the web without being required to use legacy financial institutions.
Over two decades, failed attempts at creating digital money paved the way to a reckoning and the silent launch of an open-source software project on a cypherpunk mailing list, back in 2008. Satoshi Nakamoto was the unknown pseudonym who posted about the Bitcoin project with a link to its white paper explaining how it works.
It was initially understood as yet another doomed attempt to construct a digital currency by the disillusioned cypherpunk community. Without anyone’s permission, Bitcoin slowly emerged and diligently grew to be adopted by a small group of computer researchers, cryptographers and engineers curious to decipher the technology.
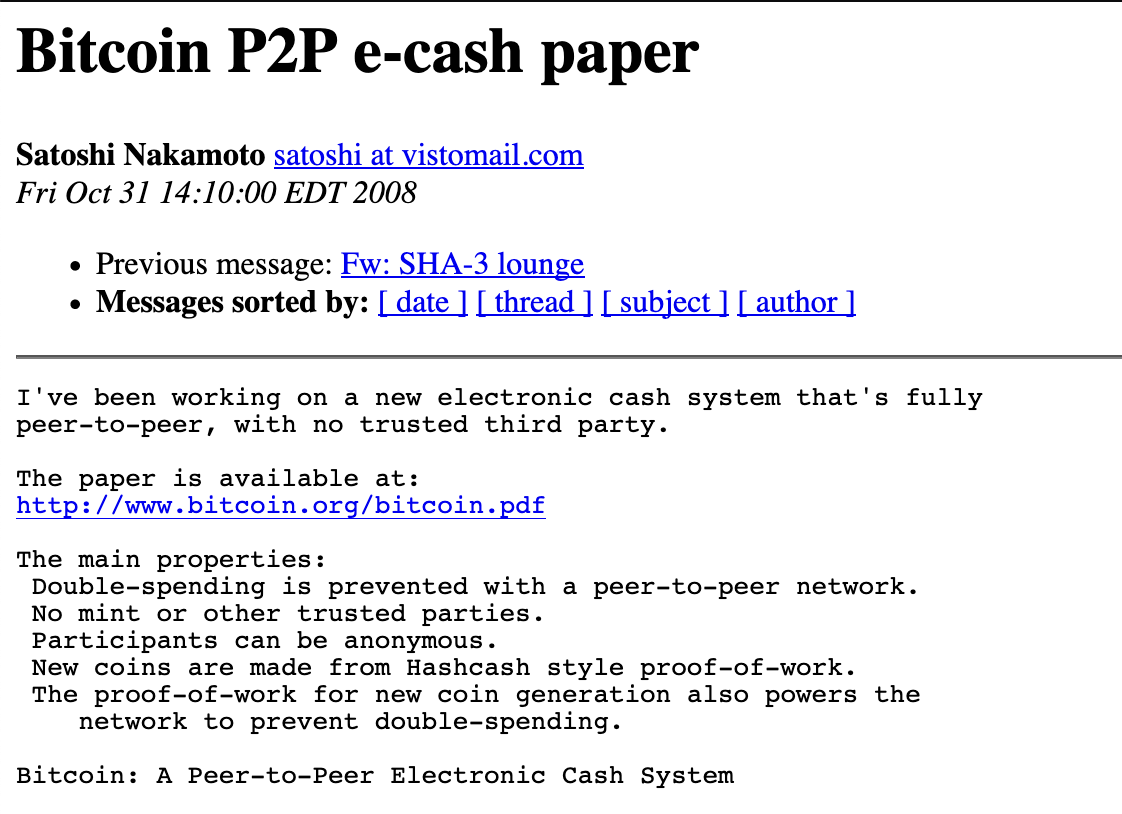 Source: Bitcoin P2P E-Cash Paper Mailing List
Source: Bitcoin P2P E-Cash Paper Mailing List
Fast forward 10 years, Bitcoin proved to be resilient to attacks, bugs and serious technical or political crises. There are hundreds of developers actively working on this project worth billions of dollars of market capitalization.
Bitcoin’s latest running software (0.17.1 released in December 2018) has created and maintained the world’s first form of digital scarcity. Without ever breaking the integrity of its underlying ledger, it does not rely on trusted third parties to verify everything is running well.
Everyone and anyone can take the role of verification. This had never been achieved in the past. Bitcoin solved a multi-decades long problem in computer science called the Byzantine Generals’ Problem.
BTC/LN as Public Network Protocols
Bitcoin is growing into the Internet’s native monetary layer. Functioning as a suite of public network protocols, BTC/LN, Bitcoin has undeniably scarce units of value. It is a network of storable, movable and quantifiable value.
As a self-contained economic system on the Internet, Bitcoin is powered by energy and protected by a global network of computing power that voluntarily regulates the integrity of Bitcoin’s ledger and its digitally-scarce monetary units. That self-organized configuration is unbreakable and decentralized like the internet itself.
Bitcoin and its Lightning Network (BTC/LN) are joining the ranks of other open network protocols akin to TCP/IP. Bitcoin (BTC) has movable units of scarce value that can flow within its network, similar to the Internet Protocol (IP).
The Lightning Network (LN) acts as a second layer built on top of BTC, which permits nearly instant, friction-free, and anonymous exchange of smaller units of BTC, similar to the Transfer Communication Protocol (TCP).
BTC/LN is the suite of protocols responsible for the rise of a native monetary layer of the Internet, adding a division to the OSI model’s current stack. Bitcoin represents the world’s first bytes of data with an intrinsic financial value priced by the physical world, in the form of energy and perceived market value.
Software now has a built-in price tag. Code is valuable without any specific application because of its remarkable scarcity. Scarcity isn’t a concept that is limited by physical boundaries anymore. Scarcity can provably be digital. It now exists in the most intangible form–bytes–digital binary digits.
A Silent Monetary Evolution
Bitcoin is agnostic of any traditional institutions such as governments, central banks or for-profit corporations. Internet users can simply acquire, trade and use bitcoins as they see fit. No single entity controls its protocol. It is governed by open-source software, which is voluntarily run by tens of thousands of independent computers.
Computers in the network play two roles around Bitcoin’s ledger, called the Timechain, by either writing or reading transactions. Bitcoin’s Timechain is a chain of blocks, which transcribes a suite of bundled transactions that are recorded by one set of computers: miners.
Often coined ‘the blockchain’, which is for other cryptocurrencies trying to mimic Bitcoin, the Timechain is more accurate to describe Bitcoin’s ledger as it ties to the original semantic used by Bitcoin’s creator, Satoshi Nakomoto.
A Free Market of Rational Volunteers
Miners are powerful computers with specialized hardware dedicated towards writing transactions to Bitcoin’s ledger. In a collective computational contest, vast amounts of energy are expensed by miners to brute-force random alphanumeric strings in an effort to guess a random code. It’s akin to a digital lottery.
Bitcoin miners’ contributions to the network are measured as hash rate, which is a function of computational power.
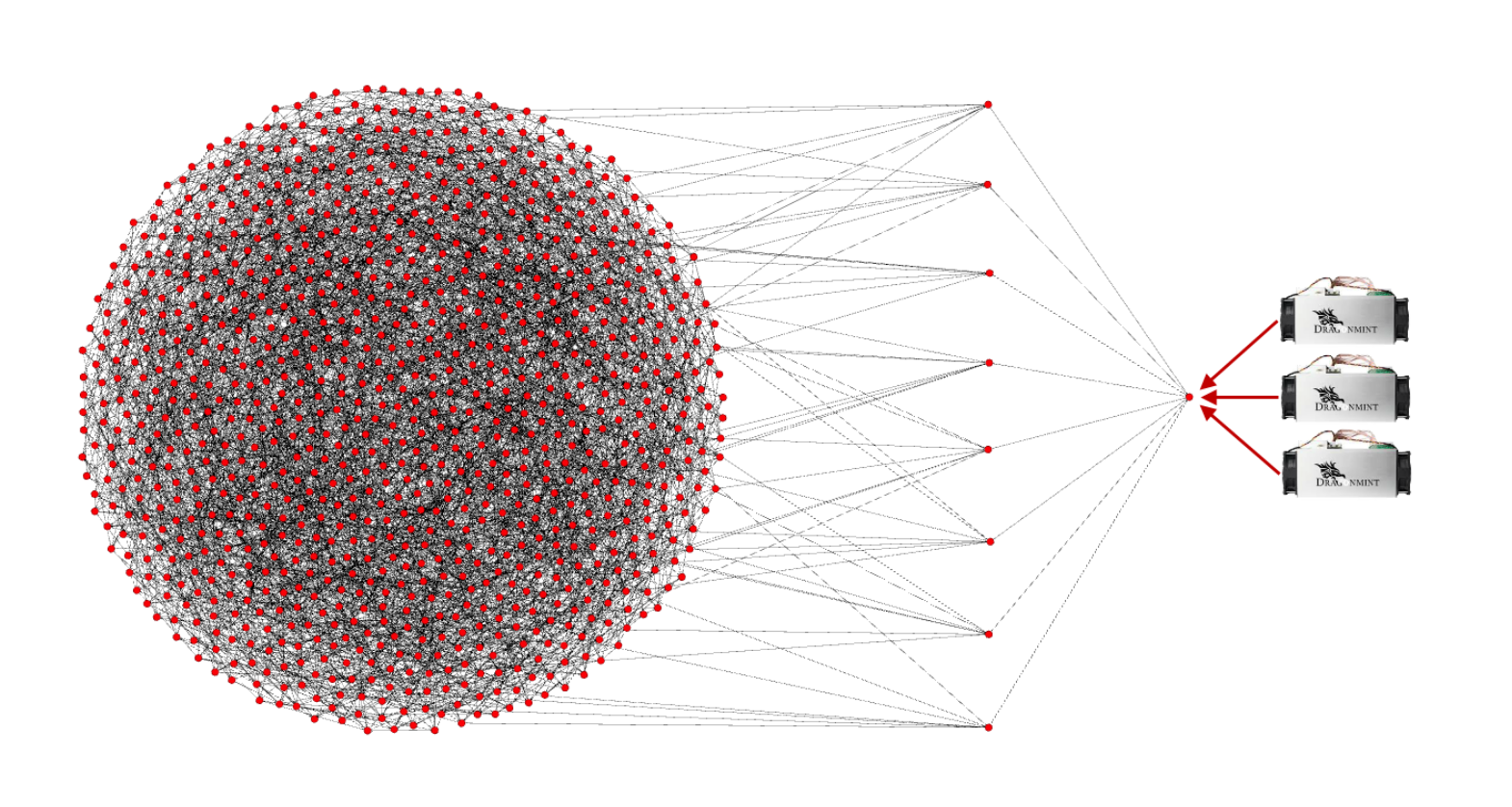 Source: Bitcoin Miners Beware: Invalid Blocks Need Not Apply
Source: Bitcoin Miners Beware: Invalid Blocks Need Not Apply
Once that random code, called a ‘nonce’ is found by a computer in the network, it proves that the miner has completed enough work in the form of energy and time expended. This is commonly referred to as Proof of Work, which allows all computers in the Bitcoin network to verify that the system stays fair and honest.
The lucky computer, or mining pool as they often combine computing power for efficiency, can then gather a batch of unconfirmed transactions from a queue called the ‘mempool’ and bundle them into a block to permanently write that block of transactions into Bitcoin’s ledger.
To be granted permission to write on Bitcoin’s ledger, there is no shortcut such as political influence, hierarchy or seniority. Each participant adding information to Bitcoin’s ledger needs to earn it through proven work that they must show to the network using the random nonce.
In return for their service to the network, miners receive a ‘block reward’ with new bitcoins, including transaction fees that users previously paid to have their transactions recorded. This is the only way for new bitcoins to be created. It must be earned via provable energy expenditure.
Since 2018, Bitcoin has shifted the world into an era of exahash computing. If one were to gather the 500 top supercomputers, altogether they would only represent 1.6% of Bitcoin’s hashrate. It is dwarfing the world’s computing horsepower by multiple orders of magnitude, creating a robust computational defense mechanism, preventing malicious actors from controlling the network and double spending bitcoins using the majority of the hashrate (often called a 51% attack).
A Self-Managed Computing Organism
Bitcoin’s ledger is secured and managed by cryptography. On average, a new block of transactions is added every 10 minutes, no matter what. Each time, this creates new bitcoins on the network, in the form of a block subsidy for the lucky miners.
The block subsidy used to be 50 bitcoins, which got cut in half in 2012, in 2016, and soon will be cut in half again in 2020, bringing the next block subsidy down to 6.25 bitcoins. This process is called halving.
Halving events happen every 210,000 blocks that are added to Bitcoin’s ledger. It is the only rule that controls the issuance of new bitcoins. It will continue roughly every 4 years until all 21 million bitcoins are mined, which should happen approximately in the year 2140.
The creation rate of new bitcoins slows down over time, until it ultimately turns to zero. No new bitcoins will be created after that moment. As new adoption increases demand, bitcoins’ price goes up too. Opportunistically, new computers are attracted to the Bitcoin network to mine blocks of transactions and receive the valuable block reward.
As more computers join the network and produce larger collective hashrate, Bitcoin is automatically adjusting the difficulty of the mining lottery. Roughly every 2 weeks, or 2,016 blocks, mining either becomes harder or easier based on how much hashrate there is.
It is the most reliable way to have new blocks mined roughly every 10 minutes, which keeps new bitcoins’ issuance highly stable and predictable, regardless of the network’s collective hash rate.
Towards Universal Financial Integrity
Since its first block mined on January 3rd, 2009 by Satoshi Nakamoto, Bitcoin has been up 99.98% of the time, and has never validated a malicious or wrong transaction, which is unprecedented for financial institutions.
This is only possible because verifying Bitcoin transactions is very accessible. While writing new transactions on the ledger is extremely costly, reading them to verify the integrity of the ledger is easy and accessible to all.
Full-validating nodes can be operated on computers less powerful than what anyone has at home or at work, making it trivial and affordable to verify the history of the Bitcoin transactions. Anybody can run them. This makes Bitcoin an impenetrable fortress of security as everyone can check every single transaction that ever happened in Bitcoin. It’s an openly auditable ledger.
Miners and full-node operators voluntarily run a version of the Bitcoin software that is compatible with the majority of the network. This maintains a general consensus on the shared rules of the network such as the block size, which dictates how many transactions can be included in a block by miners.
Large miners are incentivized to grow the size of blocks to include more transactions, gaining additional fees and making it more costly for newcomers and small participants. Full node operators choose voluntarily to run a version of the software to keep block size small to make verification accessible to everyone.
Miners have to be compatible with full-nodes to have the mined blocks be verified and approved. If Bitcoin’s block size grows, more powerful computers are required to run full-nodes with extra memory and bandwidth, which will centralize verification, adding a level of trust in the system, especially around miners.
Bitcoin’s current block size is 1MB, and has been challenged many times in the past. The most serious attack was in 2017 under the form of a fork, called Bitcoin Cash (BCH), which copied Bitcoin’s software and transaction history, and adjusted the code to raise the block size to 4MB.
Deviations such a Bitcoin Cash are the unavoidable by-product of the open-source nature of Bitcoin, which lets anyone create forked projects of Bitcoin’s Timechain, though the market continues to value these forked tokens at a substantially discounted value.
The Internet-Native Monetary System
Bitcoin (BTC) has recently seen the deployment of Lightning Network (LN), which is a layer built on top of Bitcoin to enable fast, cheap and anonymous payments. BTC is the base layer, or Layer 1. LN is the second layer, also referred to as L2. BTC and LN interoperate in a cryptographically secure manner.
LN is a network of nodes for routing payments that lets people send sats (subunits of bitcoins) where 1 BTC = 100,000,000 sats. It is much cheaper to use LN for smaller amounts instead of using BTC’s on-chain network because transactions aren’t replicated by a global system of miners and nodes to be preserved for eternity in the Timechain.
On the Lightning Network, transactions occur directly between peers, and only occasionally settle on-chain if needed as an arbitration system.
Under beta release, the Lightning Network was deployed in 2018 and has since seen a massive growth in its utilization with over 8,000 public nodes connected to the network, around 40,000 channels connecting them and more than $5 million of liquidity. One day, as LN matures, it may very well power the world’s commerce, exchanging trillions of dollars of value in today’s terms.
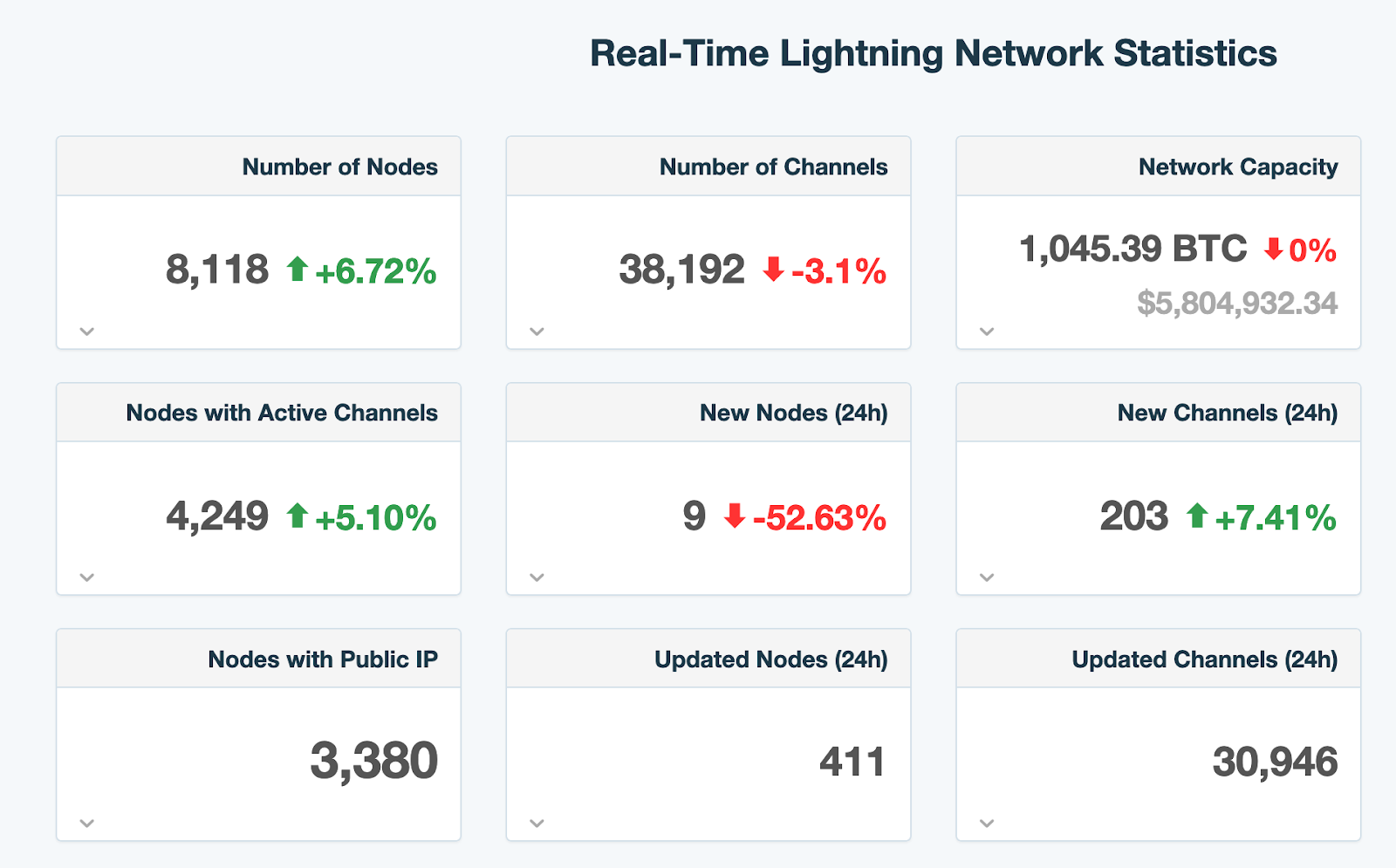 Source: 1ML
Source: 1ML
Intrinsic BTC/LN properties let people store, exchange, and measure value on the Internet. These three functions are the primary use cases for standard money we use today for our everyday lives. It just exists natively on the Internet, available to anyone with a connection.
Bitcoin and Lightning Network are two public protocols that are undeniably morphing into native Internet money, but it is still incredibly early.
Infrastructure is in its infancy, following a steady increase in global adoption with now a few millions of people using Bitcoin. Many improvements on both the base and second layer are made around privacy, security, and performance.
Beyond Bitcoin and Lightning Network
As the Internet liberated free information between global peers, Bitcoin is liberating capital exchange, creating open, fair, and social markets in which anyone can participate.
New companies exclusively built on Bitcoin’s base layer and/or Lightning Network are making it safer and easier for sovereign people to opt-out of the legacy banking system.
As trust-minimized agents, companies building the “Layer 3” of Bitcoin and Lightning Network are pushing for reasonable adoption with ethical principles and a core focus on security, usability and sovereignty.
Whether working on non-custodial private key management, LN channel capacity distribution, protocol implementations, or peer-to-peer BTC exchanges, L3 companies make the capital flow from the legacy banking system into Bitcoin possible.
L3 companies are creating massive economic upside potential for this new Internet monetary layer and will be building a Bitcoin-based economic system in the next 20-30 years without a doubt.
As always, major thanks to a few Bitcoiners who helped out with reviews, edits and suggestions. @mrcoolbp @zanepocock @theonevortex @alan_btc @Joss_do_it_BTC @anbuteau @allenshashaty